There is no software that can be considered to be truly hack proof. There are flaws in every system and it’s just a matter of how much effort is required to be able to hack into it. In the case of Apple’s Mac OS High Sierra, this bar has been set pretty low, since it is extremely easy to hack into it.
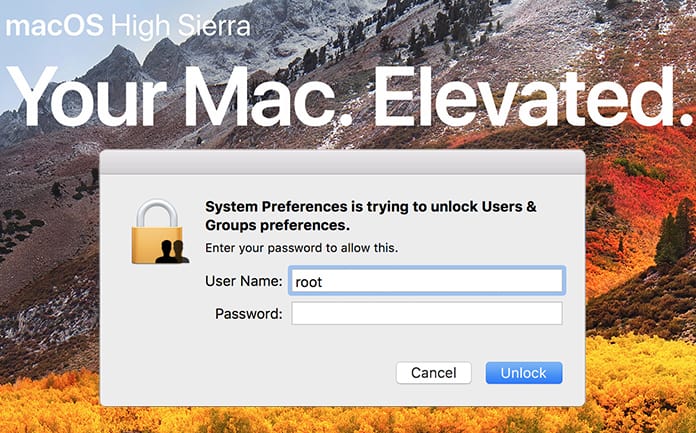
Security researchers showed a bug that reveals an extremely simple method to bypass the operating system’s security. When you go to the prompt in High Sierra it will ask for a username and password before allowing you to log in; this is true for a computer with multiple user accounts. A username and password are also required when installing a new application or even when changing the settings.
Hacking MacOS High Sierra by Typing ‘Root’
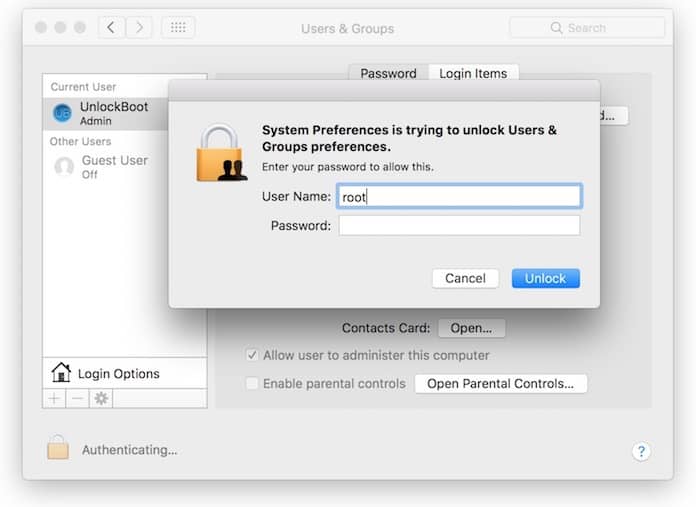
The simple hack is to use ‘root’ as a username and leave the password field blank. After doing so just click on the unlock button twice and you will be put through to provide you full access to the machine.
For those who have not grasped the gravity of this discovery, what this means is that it is now possible for any random person to turn up and open up your laptop or computer. They will be capable of accessing every nook and cranny of your device, all without any password required. These are known as ‘root’ privileges and with them, it is possible to do something like installing malware or other viruses deep in the operating system.
As the news of this security flaw began to spread across the net and social media like wildfire, there were a few security experts who found that it wasn’t possible to replicate this feat. However, there are still many different videos and GIFs that show the contrary with laptops and computers being unlocked in this manner.
The different possibilities don’t end here. It could be possible for someone to hack into a computer that is logged out and after accessing it gain root access to the machine. After they successfully accomplish this, it will only be a small matter before they could come again later and access the machine again whenever they wish and do whatever they wish.
About 18 hours after this bug had become quite famous, Apple came out with a security update that was supposed to fix this ‘root’ flaw. It was stated that a logic error was present in the validation of the credentials and Apple’s update was a word for word: ‘This was addressed with improved credential validation.’
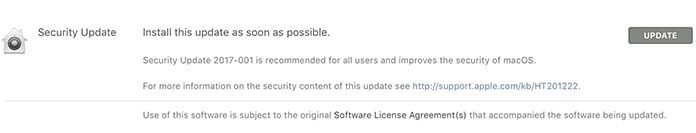
Before Apple could make the patch available, many researchers noticed that it was possible to block the attack by just setting a password for the root user. However, at the end of the day, the safest option is simply to install the new Apple update. In case you were unaware, use High Sierra and still haven’t updated, now is the perfect time to do so.
The Turkish software developer Lemi Orhan Ergin was the first person to reveal the bug. It was reported that he stumbled onto the glitch when he was trying to help a user regain access to their account. As word spread and it was tried on different machines it became obvious that it was more than just a coincidence.
In addition, this is becoming a pattern instead of a one off for High Sierra. On launch day for the operating system, it was found that malicious code was present in the OS that could steal the keychain’s contents without a password. There was another case of a bug that showed the user’s password as a hint when trying to unlock an encrypted partition on the machine known as an APFS container.
One solution could be for Apple to announce a ‘bug bounty’ where anyone who reports such anomalies and bugs or hacks is generously rewarded. The alternative is a serious security risk for all their users.
Your thoughts?










![30 Best Cydia Repo Sources For iOS 16/15/14 Jailbreak [2024] best cydia sources 2020](https://cdn.unlockboot.com/wp-content/uploads/2020/06/cydia-sources-13-100x70.jpg)